shark on wire is a forensics challenge worth 150 points.
The description of the challenge is:
We found this packet capture. Recover the flag.
This challenge provides a packet capture named capture.pcap
Opening this capture with Wireshark shows, I see that there are 2317 packets. This isn’t a lot, but its more than I want to manually review. Scrolling through the capture shows a lot of local network traffic that is probably not related to the challenge such as LLMNR, MDNS, and other such nonsense.
Since I know the flag format is picoCTF{}, I tried to do a simple search for pico by using Edit -> Find Packet. I made sure to select the Packet bytes option from the dropdown menu in the upper left. This yielded a hit on packet number 55:
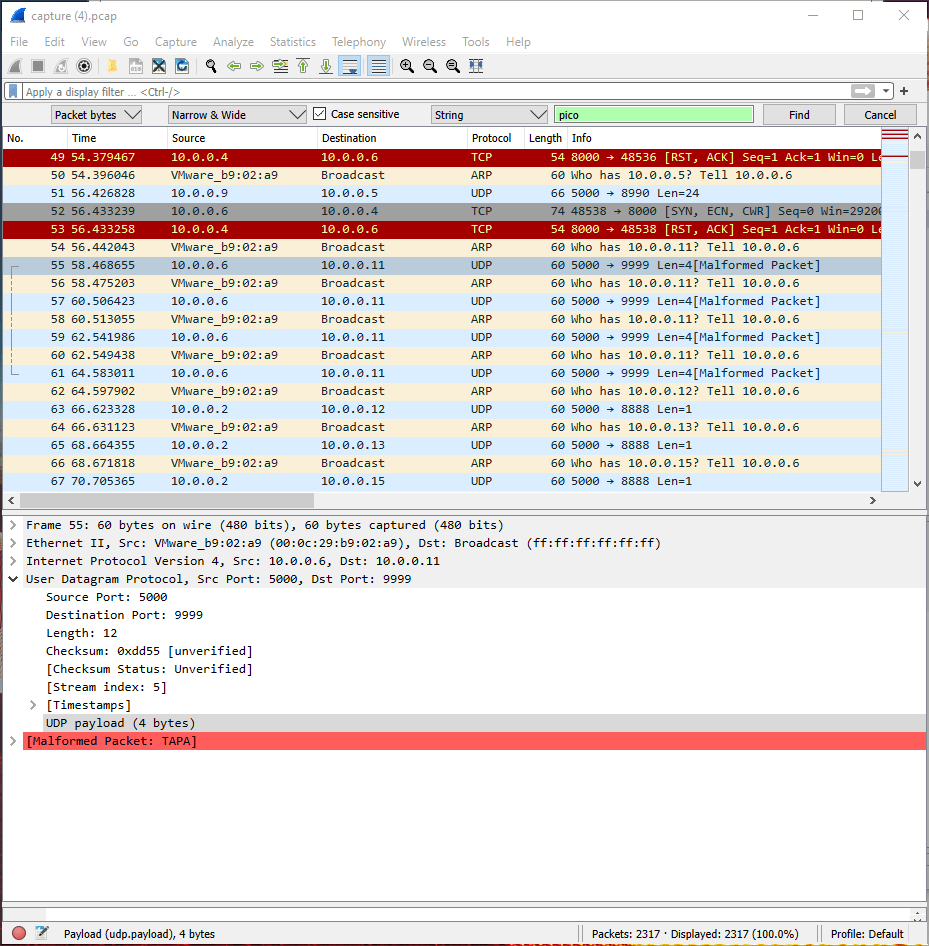
Right clicking this packet and selecting Follow -> UDP Stream didn’t give the flag, but it was interesting:

Scrolling down a little further in the capture, I saw several one byte UDP packets:

I picked a random packet in this list, right clicked on it, and selected Follow -> UDP Stream. This gave me a string that looked like the flag, but wasn’t the solution:
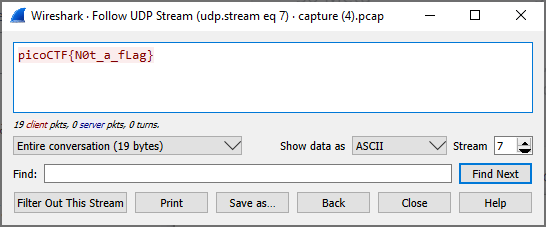
Next, I started going through the UDP streams one by one, starting at 1 within the Stream dropdown in the dialog above. At stream number 6, the flag is revealed:


Pingback: picoCTF 2019 shark on wire 2 Writeup – DMFR SECURITY
Pingback: picoCTF Writeups – DMFR SECURITY