shark on wire 2 is a forensics puzzle worth 300 points.
The description provided is:
We found this packet capture. Recover the flag that was pilfered from the network.
This challenge provides a packet capture capture.pcap.
First, I tried opening this file with Wireshark and explored its contents in a similar manner as shark on wire 1. This was outlined in a previous post: picoCTF 2019 shark on wire 1 Writeup
After looking at all the UDP streams, nothing jumped out as the flag. nothing stood out and no flags were found. I also tried just running strings on it and got some results, but no flag:

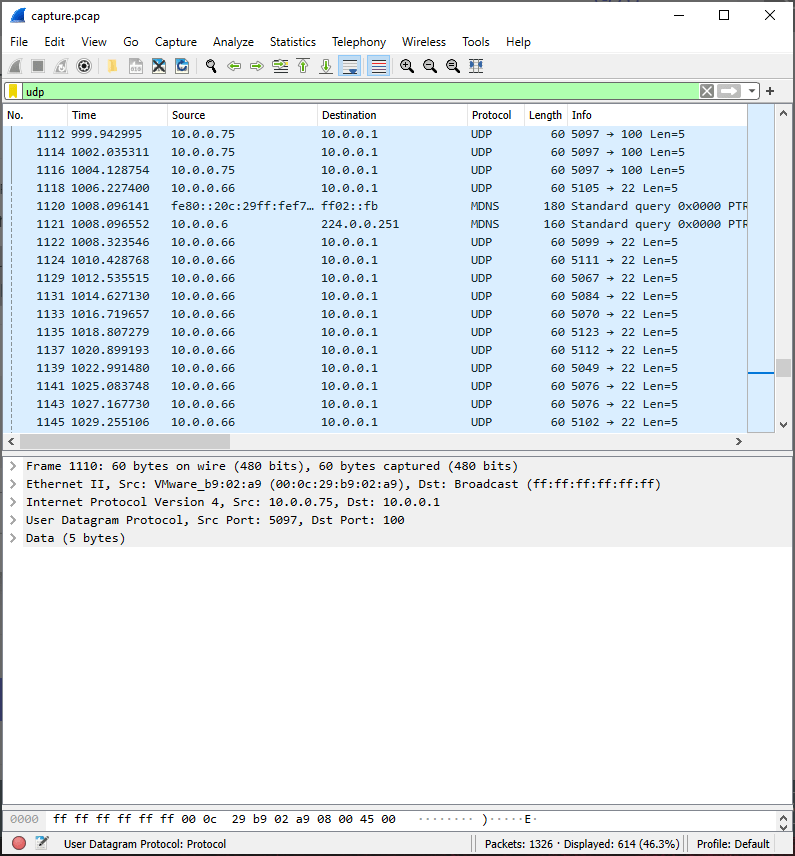
After playing around with different filters within Wireshark, I noticed most of the UDP traffic within the capture had source ports of 5000 and destination ports of 8990 and 8888. Around packet number 1104, this changes and looks somewhat random:

The traffic with the destination port of 22 looks to be the most interesting:
I didn’t want to write all of these down by hand, I don’t know of a great way to do this with Wireshark, and I’m not great at using tshark, so I used tcpdump to extract these destination ports. I whipped up this ugly one-liner to get the source ports:
% tcpdump -nr capture.pcap "udp and port 22" |awk {'print $3'} |cut -d . -f 5 |tr '\n' ' '
reading from file capture.pcap, link-type EN10MB (Ethernet)
5000 5112 5105 5099 5111 5067 5084 5070 5123 5112 5049 5076 5076 5102 5051 5114 5051 5100 5095 5100 5097 5116 5097 5095 5118 5049 5097 5095 5115 5116 5051 5103 5048 5125 5000 %
It is interesting that this starts and ends with port 5000. This likely signals the start and end of the message. Having done so many CTFs and looking at malware that uses charcode encoding so much at work, I recognize this as charcode encoding, with an extra 5 or 50 prepended.
I made my one-line even uglier, editing out the prepended 5 and 0 with sed:
% tcpdump -nr capture.pcap "udp and port 22" |awk {'print $3'} |cut -d . -f 5 |sed 's/^5//g' |sed 's/^0//g' |tr '\n' ' '
reading from file capture.pcap, link-type EN10MB (Ethernet)
00 112 105 99 111 67 84 70 123 112 49 76 76 102 51 114 51 100 95 100 97 116 97 95 118 49 97 95 115 116 51 103 48 125 00
Omitting the leading and trailing null characters, I pasted 112 105 99 111 67 84 70 123 112 49 76 76 102 51 114 51 100 95 100 97 116 97 95 118 49 97 95 115 116 51 103 48 125 as input into CyberChef, and used the From Charcode operation to decode the flag:


Pingback: picoCTF Writeups – DMFR SECURITY