REVIEW: RED TEAM Operator: Malware Development Intermediate Course by SEKTOR7 Institute.
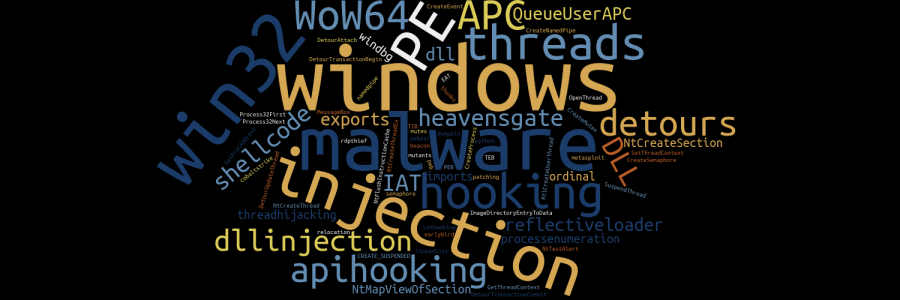

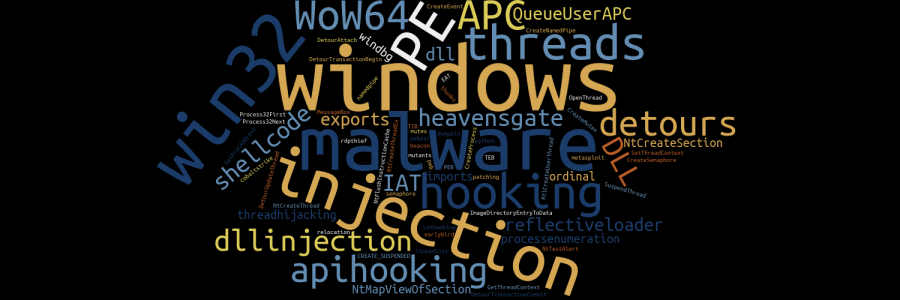
REVIEW: RED TEAM Operator: Malware Development Intermediate Course by SEKTOR7 Institute.

REVIEW: RED TEAM Operator: Windows Evasion Course by SEKTOR7 Institute.
picoCTF 2019 flag_shop writeup.
Quick and dirty example of process enumeration using CreateToolhelp32Snapshot
Quick example of using WTSEnumerateProcesses to enumerate processes running on a Windows machine.
Find malware running from temporary directories using procfs.

Find masquerading processes using procfs.

My review of SEKTOR7 Institute's Red Team Operator, Windows Persistence course.
Exit values on Windows are much more robust than on *nix systems. Here are some notes about exit values on Windows