WebNet1 is a forensics puzzle worth 450 points.
The description provided is:
We found this packet capture and key. Recover the flag.
This puzzle presents a packet capture capture.pcap and a key: picopico.key
I did this puzzle immediately after solving WebNet0. The key was the same as WebNet0:
% md5sum picopico* 57a3d0809b40857e71cbe069cda58829 picopico (1).key 57a3d0809b40857e71cbe069cda58829 picopico.key
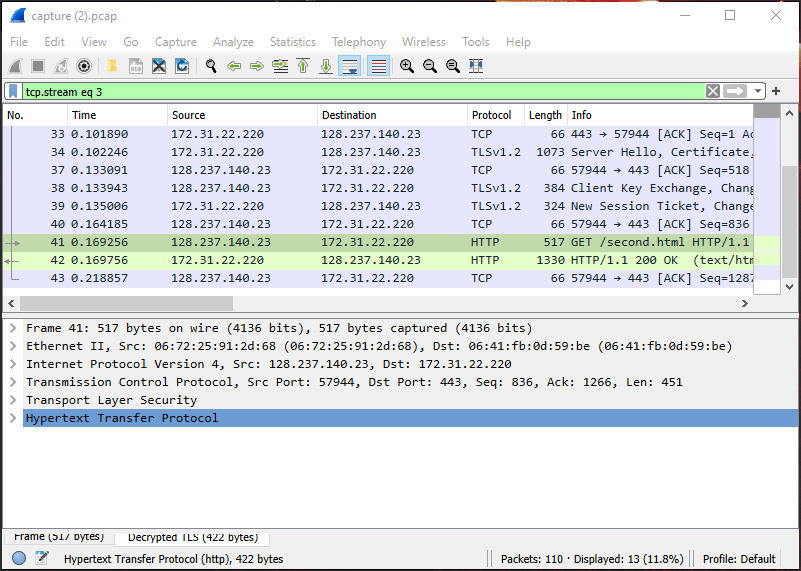
Wireshark was already configured to use this key, so I didn’t have to configure Wireshark to use the key. These configuration steps are documented here: picoCTF 2019 WebNet0 Writeup
After opening the packet capture, right click on the first HTTP packet and select Follow -> HTTP Stream
This stream shows a different flag in the header this time: Pico-Flag: picoCTF{this.is.not.your.flag.anymore} I took their word for it and looked through the stream a bit further and found the flag:


Pingback: picoCTF Writeups – DMFR SECURITY