Find samples containing registry run key pathways with YARA.
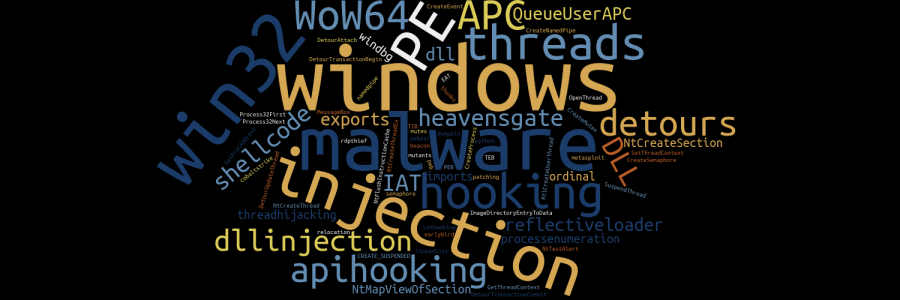
Category: windows
REVIEW: Reversing: Secrets of Reverse Engineering
Book review of Reversing: Secrets of Reverse Engineering.
REVIEW: Practical Malware Analysis: The Hands-On Guide to Dissecting Malicious Software
My review of Practical Malware Analysis.
Accessibility Features Persistence
Abusing Accessibility Features as a persistence mechanism.
Malicious LNK Files
Malicious LNK files.
Scheduled Task Persistence
Some notes on finding malicious Scheduled Tasks.
Get-ChildItem Performance
I was writing some PowerShell scripts to scan disks for certain types of malware and realized that Get-ChildItem was kind of slow. I googled around and found this site which demonstrated using robocopy.exe and dir as faster alternatives to Get-ChildItem. Here were the results I had searching for LNK files on my disk using both …
Installing OLE Tools on Windows
Installing OLE Tools on Windows

REVIEW: RED TEAM Operator: Privilege Escalation in Windows Course by SEKTOR7 Institute
This is my review of the RED TEAM Operator: Privilege Escalation in Windows course offered by SEKTOR7 Institute. As an affiliate, I make money with qualifying purchases. RED TEAM Operator: Privilege Escalation in Windows is a brief introduction to the subject. As with other offerings by SEKTOR7, this course expects that you know the basics of …
Remove Carriage Return (^M) Characters with Emacs
Remove carriage return, Control-M (^M) Characters with Emacs.
REVIEW: RED TEAM Operator: Malware Development Intermediate Course by SEKTOR7 Institute
REVIEW: RED TEAM Operator: Malware Development Intermediate Course by SEKTOR7 Institute.

REVIEW: RED TEAM Operator: Windows Evasion Course by SEKTOR7 Institute
REVIEW: RED TEAM Operator: Windows Evasion Course by SEKTOR7 Institute.
