Trivial Flag Transfer Protocol is a forensics puzzle worth 90 points.
This puzzle’s description is:
Figure out how they moved the flag.
This puzzle provides a packet capture tftp.pcapng.
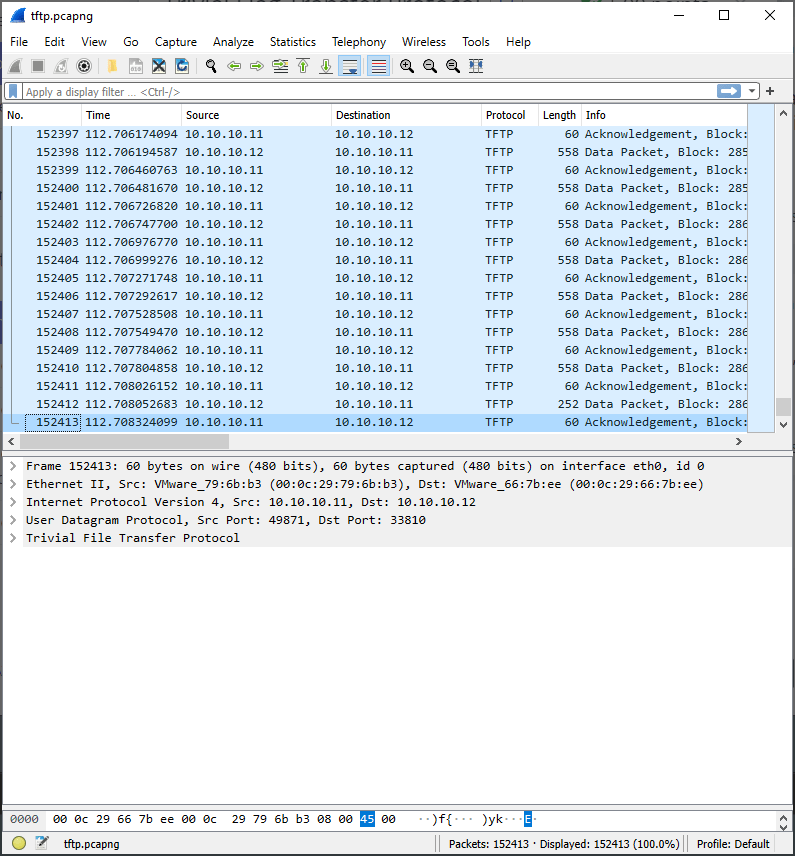
Viewing this packet capture in Wireshark shows a substantial amount of tftp traffic:
Extracting files transferred with tftp is easy with Wireshark: File -> Export Objects -> TFTP

Next, I clicked Save All and exported these files to a folder. instructions.txt and plan are text files, but they appear to be encoded or encrypted somehow. There’s also program.deb which is a Debian package, and three bitmaps.
Looking closer at instructions.txt, it appears to be a substitution cipher. More often than not, CTFs use rotation-based substitution ciphers. Plugging this into https://rot13.com decoded this text:

This revealed the following instructions:
TFTP DOESNT ENCRYPT OUR TRAFFIC SO WE MUST DISGUISE OUR FLAG TRANSFER.FIGURE OUT A WAY TO HIDE THE FLAG AND I WILL CHECK BACK FOR THE PLAN
Next, I have a look at plan, which also appears to be encoded. I plug this into rot13.com and it decodes cleanly:
I USED THE PROGRAM AND HID IT WITH - DUE DILIGENCE.CHECK OUT THE PHOTOS
program.deb is a Debian package. These can be extracted with ar:
% file program.deb program.deb: Debian binary package (format 2.0), with control.tar.gz, data compression xz % ar x program.deb
Extracting program.deb presented me with control.tar.gz, data.tar.xz, and debian-binary. First I extract `control.tar.gz`
% tar xvf control.tar.gz ./ ./md5sums ./control
control is a text file that contains the following, suggesting that steghide is the “program” referred to in plan.
% cat control Package: steghide Source: steghide (0.5.1-9.1) Version: 0.5.1-9.1+b1 Architecture: amd64 Maintainer: Ola Lundqvist <opal@debian.org> Installed-Size: 426 Depends: libc6 (>= 2.2.5), libgcc1 (>= 1:4.1.1), libjpeg62-turbo (>= 1:1.3.1), libmcrypt4, libmhash2, libstdc++6 (>= 4.9), zlib1g (>= 1:1.1.4) Section: misc Priority: optional Description: A steganography hiding tool Steghide is steganography program which hides bits of a data file in some of the least significant bits of another file in such a way that the existence of the data file is not visible and cannot be proven. . Steghide is designed to be portable and configurable and features hiding data in bmp, wav and au files, blowfish encryption, MD5 hashing of passphrases to blowfish keys, and pseudo-random distribution of hidden bits in the container data.
Re-reading the plan, they hid it with DUEDILIGENCE. This is likely the password used with steghide:
% steghide extract -p DUEDILIGENCE -sf picture1.bmp steghide: could not extract any data with that passphrase! % steghide extract -p DUEDILIGENCE -sf picture2.bmp steghide: could not extract any data with that passphrase! % steghide extract -p DUEDILIGENCE -sf picture3.bmp wrote extracted data to "flag.txt".
The flag was hidden within picture3.bmp using password DUEDILIGENCE.

Pingback: picoCTF Writeups – DMFR SECURITY